Arthur Herman
The ultimate nightmare for cybersecurity experts is someone using a quantum to factorize the large numbers that underlie our existing encryption systems, from banks and financial markets to secure access to databases around the world.
Unlike conventional hacks, such an attack would be stealthy and virtually undetectable, while cracking one encryption system essentially means cracking them all simultaneously.
It means waking up to a world where every secret and every bit of sensitive data, lies exposed to America’s deadliest foes.
That’s the scenario that haunts the federal government’s efforts in 2022 to get all federal agencies to develop a timeline as to when they’ll be quantum-safe. Meanwhile, at the QAI, we’ve partnered with Oxford Economics to publish two econometric reports on the catastrophic damage such an attack would cause for the national power grid; for the cryptocurrency market; and a new report on the possible impact on the Federal Reserve.
The urgent question has been, how soon will quantum computers be capable of such an attack—as the jargon has it, when will a “cryptographically relevant quantum computer” be a reality. Because of the big engineering challenges of lining up enough “entangled,” i.e. simultaneous working, quantum bits to do the heavy factorization lift, skeptics insist that such an event lies somewhere far off in the future, if ever.
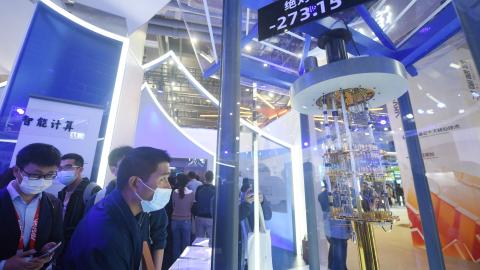
In a new paper, Chinese scientists claim they have devised an algorithm that could crack a very hard encryption nut, i.e. 2048-bit RSA, using a 372-qubit quantum computer. Their algorithm goes beyond the one authored by Peter Shor in the 1990’s which is the theoretical basis of quantum computing’s decryption capability, by using still another algorithm developed by German mathematician Claus-Peter Schnorr, who in 2022 declared it was possible to factor large numbers more efficiently than Shor’s algorithm—so efficiently you could break the RSA code even with a classical computer.
The Chinese say they’ve proved it’s possible to decrypt 2048-bit RSA, by using a classical computer with only 10 entangled qubits. That’s no mean feat given the fact that other experts said cracking 2048 RSA couldn’t be done with less than 20 million qubits, if it can be done at all.
The Chinese team insist they cracked 48-bit RSA using a 10-qubit quantum computer-based hybrid system, and could do the same for 2048-bits if they had access to a quantum computer with at least 372 qubits. That’s almost within reach of today’s quantum computers. For example, IBM’s newly announced Osprey boasts 433 qubits.
If those claims are true, then a code-breaking quantum computer is just around the technological corner. But the report has provoked plenty of doubts, some even labeling it a hoax.
Critics are rightly skeptical that the process described by Schnorr’s algorithm is truly scalable, as the report claims. The Chinese team even admits “quantum speed-up of the algorithm is unclear due to the ambiguous convergence of QAOA”, which is the quantum subroutine used to solve the prime numbers puzzle and crack RSA. This suggests they don’t know if their algorithm will work when it’s tried with larger numbers of qubits in a genuine computer.
It's a little like someone claiming he’s found a way to land a spaceship on the moon because he built a rocket in his backyard that jumped the fence into his neighbor’s yard.
Still, he may have misjudged the distance, but he has the right tools in hand.
In that sense, what the Chinese have done is directionally significant. Delving deeper into the paper, we see that their results came by using a hybrid system, i.e. one that combines classical and quantum elements for its computations. Such a system has been used before in Chinese quantum code-breaking research, which I profiled in an earlier column.
This means you don’t have to have a monolithic, large-scale quantum computer to do decryption—the theoretically error-free quantum machine that might be finally ready by 2040. With hybrid tools, you can start working on the process right now, in the era of today’s error-prone “noisy” quantum computers.
That’s why the Biden administration has been right to issue executive orders like National Security Memorandum 10 to push agencies to adopt quantum-safe standards sooner rather than later, while Congress has passed the Quantum Cybersecurity Preparedness Act, first sponsored by California Congressman Ro Khanna. At the same time, our government needs to accelerate its efforts in the race to quantum decryption, not just through quantum alone but also via the hybrid route.
Meanwhile, private companies and institutions need to accelerate their own adoption of quantum-safe solutions, for the future of their data and networks.
Because the timeline to Q-Day gets a little shorter every time.
No comments:
Post a Comment